Airtable Vs. Notion:选择您的利器以实现最高效率
airtable和notion是…

airtable和notion是…

你想在本地主机上安装wordpr…

网络杀伤链(cyber kill…

威胁。它采用了一种“不信任任何人”的策略,因此支持此策略的技术在应对增加的威胁时正得到越来越广泛的采用。

配置、监控和保护网络是系统管理员工作的重要组成部分。当涉及管理Linux网络时,有许多、和HTML标签可供使用。

testing, and IT security. These tools can help you identify vulnerabilities in computer systems, networks, and applications, and ensure that they are secure and protected against unauthorized access and attacks. Some popular tools include Metasploit, Wireshark, Nmap, Burp Suite, and Kali Linux. Additionally, there are numerous online resources, courses, and certifications available to help you develop your skills and knowledge in this field. So if you’re interested in becoming a penetration tester or an IT security expert, start exploring these resources and tools today!
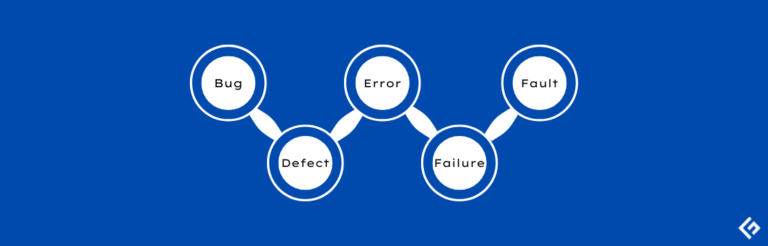
软件测试是一个用来发现错误、缺陷、故障和失败的过程,这些都是预期结果与实际结果之间的差异。
如果您在软件开发游戏中已经有一段…

动态应用安全测试(dast)扫描…
网络犯罪是各种规模和行业的企业面…